













Syncly provides a growing library of plug and play integration connectors to the technology platforms you know and love. Use them in any order, and any combination.
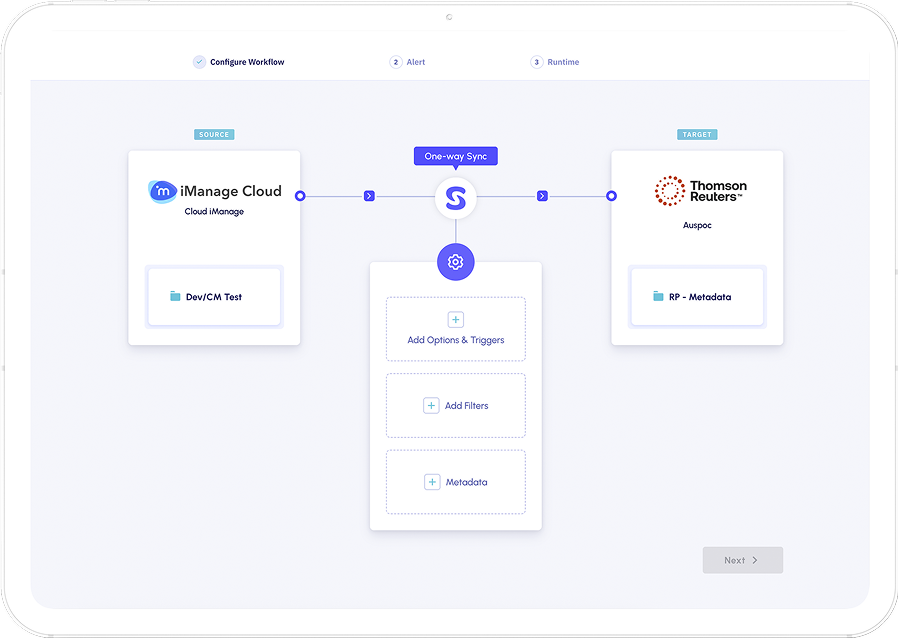
Create One and two-way sync Workflows to enable the secure movement of both documents and data in real-time. Handle document versions with robust conflict checking and error handling.
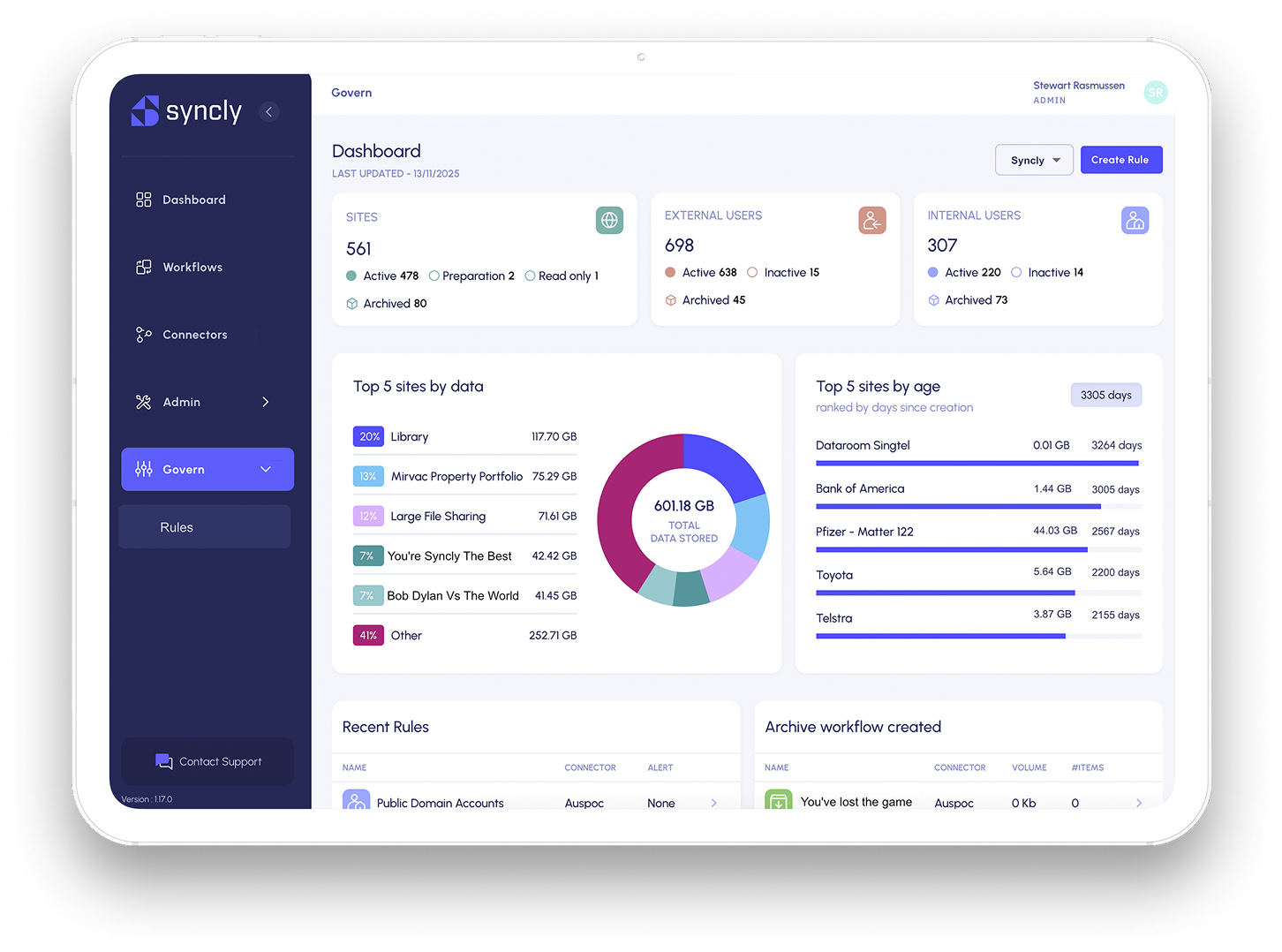
Create reports to monitor for dormant users, inactive sites, unusual behaviours and more. Enforce compliance with realtime actions such as site archival and user account suspension.
Syncly is SOC 2 Type II certified and compliant with GDPR, CCPA, and HIPAA.
We’ve built our business around these standards from the very start — we don’t just provide security, we live it.



